Bitcoin Explained: A Comprehensive Guide to Mining, Blockchain, and Transactions
This article provides a detailed explanation of the Bitcoin network, covering its fundamental principles, mining process, transaction mechanisms, and its relationship to blockchain technology. Designed for professionals, developers, and tech enthusiasts, this guide offers an objective and in-depth look into the workings of Bitcoin.
The Genesis of Bitcoin and Decentralization
In 2008, a person or group under the pseudonym Satoshi Nakamoto published a whitepaper detailing how Bitcoin could facilitate decentralized transactions without the need for financial institutions. This concept leverages blockchain technology to ensure secure and transparent peer-to-peer exchanges.
In 2009, Nakamoto developed the first Bitcoin wallet software, distributing it online. This software enables users to connect to the Bitcoin network, forming a peer-to-peer (P2P) network. Each user’s computer, running the wallet software, becomes a node in the network, capable of communicating and transacting directly with other nodes. The initial nodes, known as seed nodes, are pre-programmed into the software, allowing new users to connect and discover other nodes.
Understanding Bitcoin Addresses and Transactions
Bitcoin addresses are similar to bank account numbers, allowing users to receive Bitcoin. These addresses are generated through the wallet software and do not require a central authority. Unlike traditional banking systems, Bitcoin transactions are recorded across the network in a decentralized manner.

Each user’s wallet software allocates a portion of memory, approximately 300MB, to store transaction records. The process begins with the creation of a block, where the first transaction is a “coinbase” transaction. This transaction awards a predetermined amount of Bitcoin to the miner who successfully creates the block. Initially, this reward was 50 Bitcoins, halving approximately every four years.
The Mining Process: Securing the Blockchain
Mining is a critical process that involves validating transactions and creating new blocks in the blockchain. It requires computational power to solve complex cryptographic puzzles. Here’s a breakdown:
- Hashing: All transactions within a block are processed through a hash function, generating a unique hexadecimal string.
- Block Header: The block header contains the hash of the previous block, a timestamp, and a difficulty target.
- Proof-of-Work (PoW): Miners repeatedly calculate the hash of the block header, modifying a “nonce” value until the resulting hash meets the difficulty target.
The difficulty target is dynamically adjusted every 2016 blocks (approximately every two weeks) to maintain an average block creation time of 10 minutes. This adjustment ensures the stability and security of the network, regardless of the total computational power (hashrate) of the network.
Transaction Validation and Blockchain Formation
Once a miner finds a valid hash, they broadcast the new block to the network. Other nodes verify the block’s validity by recalculating the hash and ensuring it meets the difficulty target. If valid, the block is added to their local copy of the blockchain, and the transaction is considered confirmed.
The blockchain is a chain of blocks, each containing the hash of the previous block. This structure ensures that any alteration to a previous block would require recalculating all subsequent blocks, making it computationally infeasible to tamper with the blockchain.
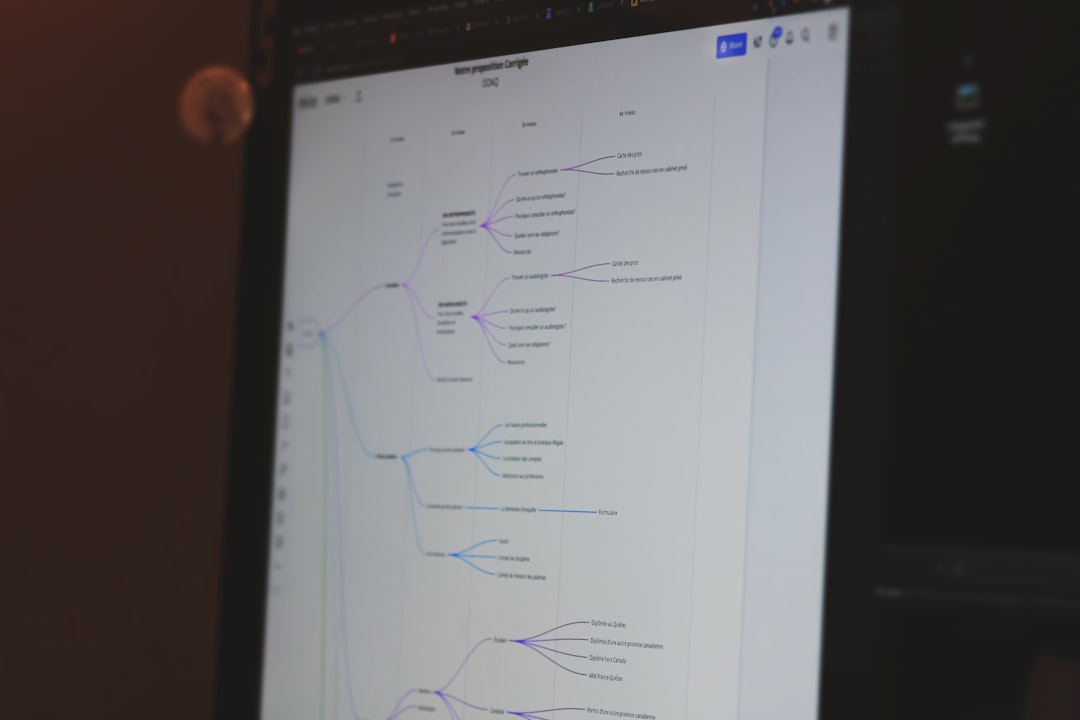
Practical Demonstration: Setting Up a Local Bitcoin Network
To illustrate these concepts, one can set up a local Bitcoin network for testing and educational purposes. This involves downloading the Bitcoin Core wallet software, configuring it to run in “regtest” mode (a local testing environment), and creating multiple nodes on a single machine.
The steps include:
- Downloading and installing Bitcoin Core from the official website.
- Creating separate directories for each node (e.g., “node1”, “node2”).
- Configuring a
bitcoin.conffile for each node, specifying network settings and RPC credentials. - Launching each node with the
bitcoind -regtestcommand. - Using the
bitcoin-clicommand-line tool to interact with each node, generating addresses, mining blocks, and sending transactions.
Addressing 51% Attacks and Network Security
A potential threat to the Bitcoin network is a 51% attack, where a single entity controls more than half of the network’s computational power. This would theoretically allow the attacker to rewrite transaction history and double-spend Bitcoins.
However, given the current size and decentralization of the Bitcoin network, achieving 51% control is highly improbable. The computational resources required would be enormous, making such an attack economically infeasible.
Conclusion
Bitcoin’s innovative approach to decentralized transactions has revolutionized the financial landscape. By understanding the core principles of mining, blockchain, and transaction validation, professionals and enthusiasts can better grasp the potential and limitations of this groundbreaking technology. Despite ongoing debates about its value and environmental impact, Bitcoin remains a secure and reliable system for peer-to-peer transactions.